On-Chain Crypto Transaction Tracing: How to Track Funds on the Blockchain
 Apr, 25 2026
Apr, 25 2026
Think your crypto transactions are invisible? Most people assume that because they don't have to enter their name or email to send Bitcoin, they're completely anonymous. In reality, blockchains are more like public ledgers where every single move is recorded for everyone to see. While your name isn't attached to your wallet, your digital footprint is permanent. This is why crypto transaction tracing is the process of analyzing blockchain data to follow the movement of funds and link digital wallets to real-world identities . Whether it's a government agency chasing a ransomware payment or a trader analyzing a "whale," the goal is the same: turning a string of random characters into a clear story of who sent what, when, and where.
The Core Logic: Pseudonymity vs. Anonymity
To understand how tracing works, you first have to accept that most cryptocurrencies are pseudonymous, not anonymous. This means that while your identity is hidden, your wallet address is public. If you ever link that address to a real-world identity-say, by sending funds to a centralized exchange that requires a passport for KYC (Know Your Customer)-the veil is lifted. Once one address in a chain is identified, investigators can often work backward and forward to map out your entire financial history.
Common Tracing Methodologies
Experts don't just stare at a block explorer and guess; they use specific technical frameworks to categorize movements. Most current tracing falls into three buckets:
- Heuristic-based techniques: These are basically "educated guesses" based on common patterns. For example, if a wallet sends funds to five different addresses at the exact same time, a heuristic might suggest those five addresses belong to the same person. These are great for simple, single-chain moves, with some platforms hitting nearly 90% accuracy on networks like Ethereum.
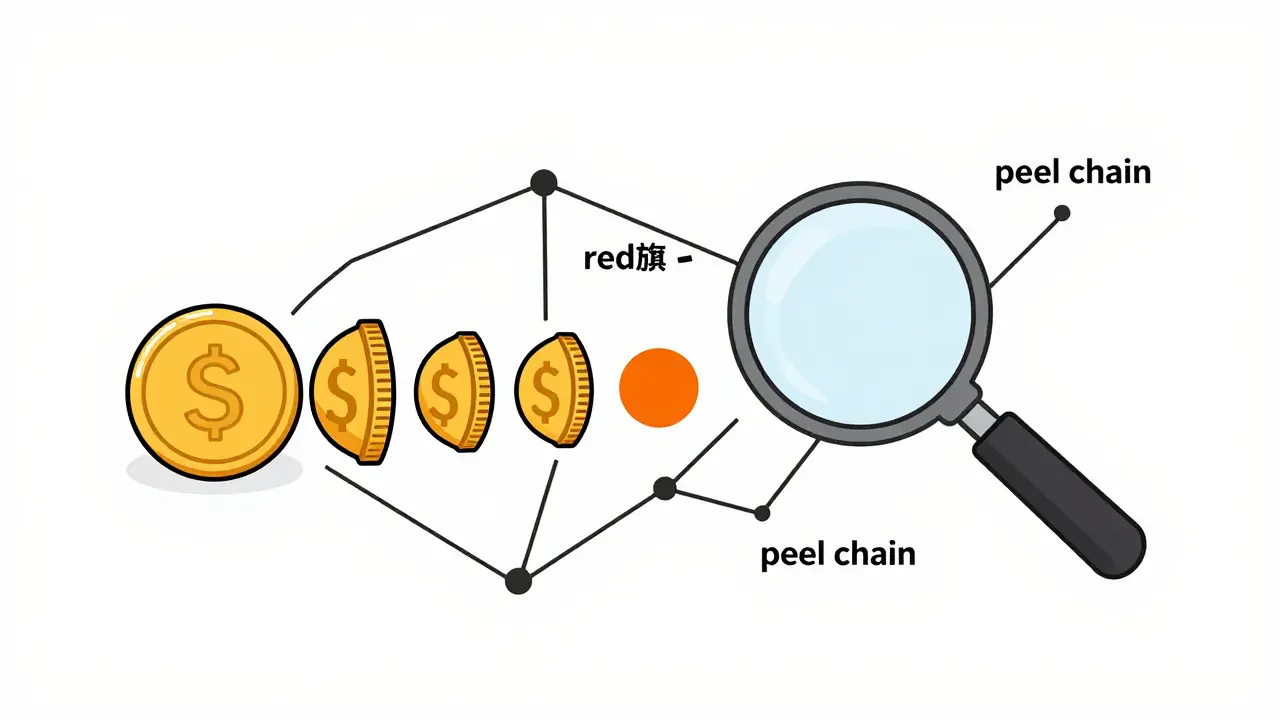
- Rule-based techniques: These look for specific "red flags." One classic example is a peel chain, where a large amount of crypto is sent to a new address, a small amount is "peeled off" to an exchange, and the rest is sent to another new address. This is a common tactic used to hide the origin of funds.
- Graph learning-based approaches: This is the cutting edge. Instead of simple rules, these systems use machine learning to treat the blockchain as a massive web (a graph). They can spot complex patterns that a human would miss, making them far more effective for "multi-hop" tracing where funds jump through several wallets to confuse observers.
| Method | Best Use Case | Primary Strength | Major Weakness |
|---|---|---|---|
| Heuristics | Single-chain moves | Fast and simple | Low cross-chain accuracy |
| Rule-Based | Detecting peel chains | High pattern detection | Easily bypassed by new tactics |
| Graph Learning | Complex fund flows | Handles multi-hop jumps | High compute requirements |
Advanced Tactics for Investigators
When simple tracing isn't enough, forensics experts use a few specialized tricks to break through obfuscation. One of the most powerful is wallet clustering, which is the process of grouping multiple addresses into a single cluster that represents one entity. They do this through "common spend analysis"-if two different addresses are used as inputs in a single transaction, it's almost certain that one person controls both.
Other tactics include IP correlation, where analysts try to match the timing of a blockchain transaction with a specific IP address hitting a node. While this is incredibly difficult and often requires cooperation from ISPs or exchanges, it's a gold mine for definitive attribution. They also look for dusting attacks, where tiny amounts of crypto are sent to wallets to "mark" them and track where those funds eventually move.
The Cross-Chain Challenge
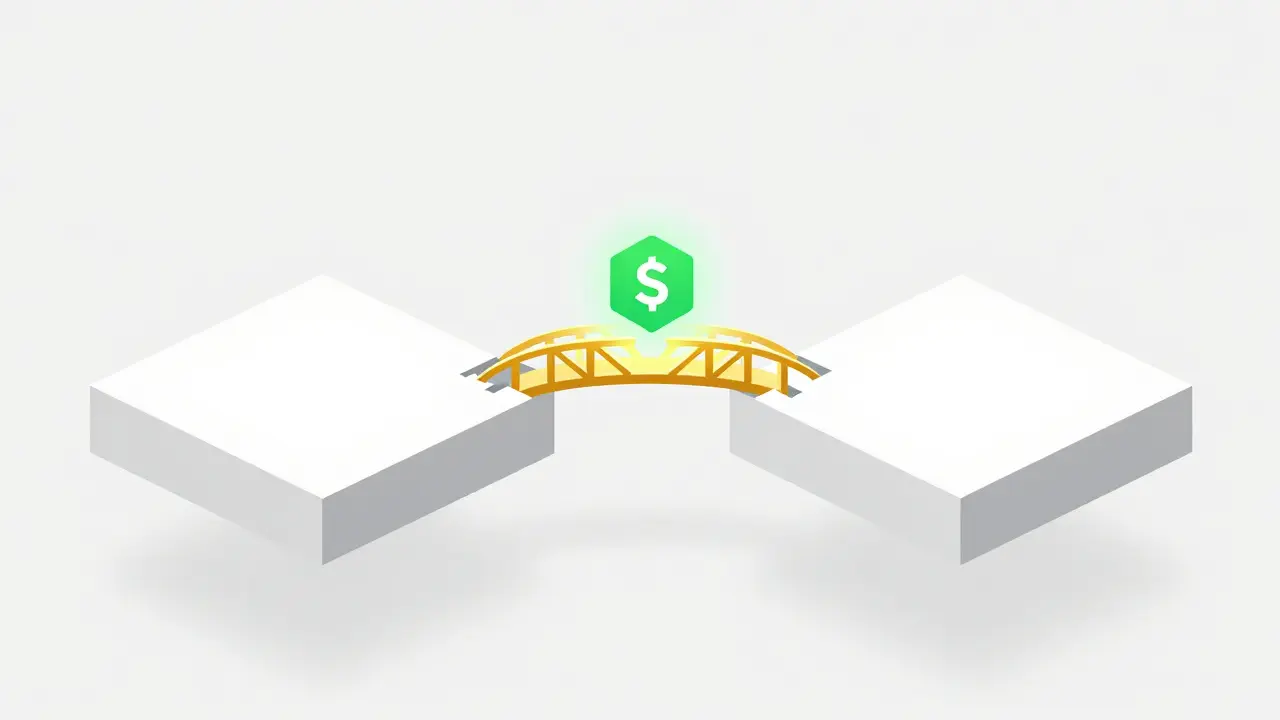
The biggest headache for any analyst today is the "chain hop." Sophisticated users don't just stay on Ethereum; they use cross-chain bridges to move assets to networks like Tron or Binance Smart Chain (BSC). Every time funds cross a bridge, the trail effectively "breaks" because the investigator has to leave one blockchain and find the corresponding transaction on another.
For instance, a hacker might lock ETH in a bridge contract and mint a wrapped version of that asset on another chain. If the investigator doesn't understand the specific bridge mechanics (lock-and-mint vs. swap), they lose the scent. This is why professional tools now focus heavily on automated cross-chain tracing, though these services often come with a hefty price tag, sometimes exceeding $25,000 a year per user.
Obstacles to Tracing: The Privacy Arms Race
It's not all easy for the trackers. There is a constant "cat-and-mouse" game happening. Criminals and privacy advocates use privacy coins like